Server-Side Tracking: What It Fixes and What It Doesn't
Show article contentsHide article contents
- What server-side tracking actually is
- The 27-store audit
- What server-side tracking does fix
- What server-side tracking cannot touch
- The Shopify origination gap
- What the rescue-pipe ecosystem actually costs in 2026
- The EMQ ceiling
- The decision framework
- Origin-first: what the architecture looks like when events come from the server by design
- The honest verdict
- Frequently asked questions
- Stop paying for the relay
Server-side tracking is sold as the fix for every modern ecommerce data problem. We re-audited 27 top DTC Shopify brands. One of them uses it. And in more than half the sample, it wouldn't have mattered even if they did. The reason is not cost and it is not complexity. It is that the events server-side tracking is supposed to rescue never originated in a place it could reach.
- In an April 2026 re-audit of 27 top DTC Shopify brands, 1 of 27 had any server-side pipe installed: one Littledata. Zero Elevar, Stape, Analyzify, or custom-subdomain sGTM.
- Server-side GTM is a transport relay. If Shop Pay, Apple Pay, PayPal, iframe checkouts, or a consent rejection prevent the event from firing, sGTM has nothing to forward.
- Honest 2026 managed-stack cost on Shopify: $475 to $970 per month ongoing plus $1,000 to $2,790 setup. Google Cloud Run alone runs $150 per month minimum.
- 51.9% of audited stores run Meta Pixel client-side and route checkout to an external Shopify domain. sGTM cannot close this gap: the purchase event never originates in merchant JS.
- In Germany and France, roughly 40% of visitors reject cookies. Server-side tracking recovers zero of those sessions. Consent suppresses the tag fire before any request leaves the browser.
What server-side tracking actually is
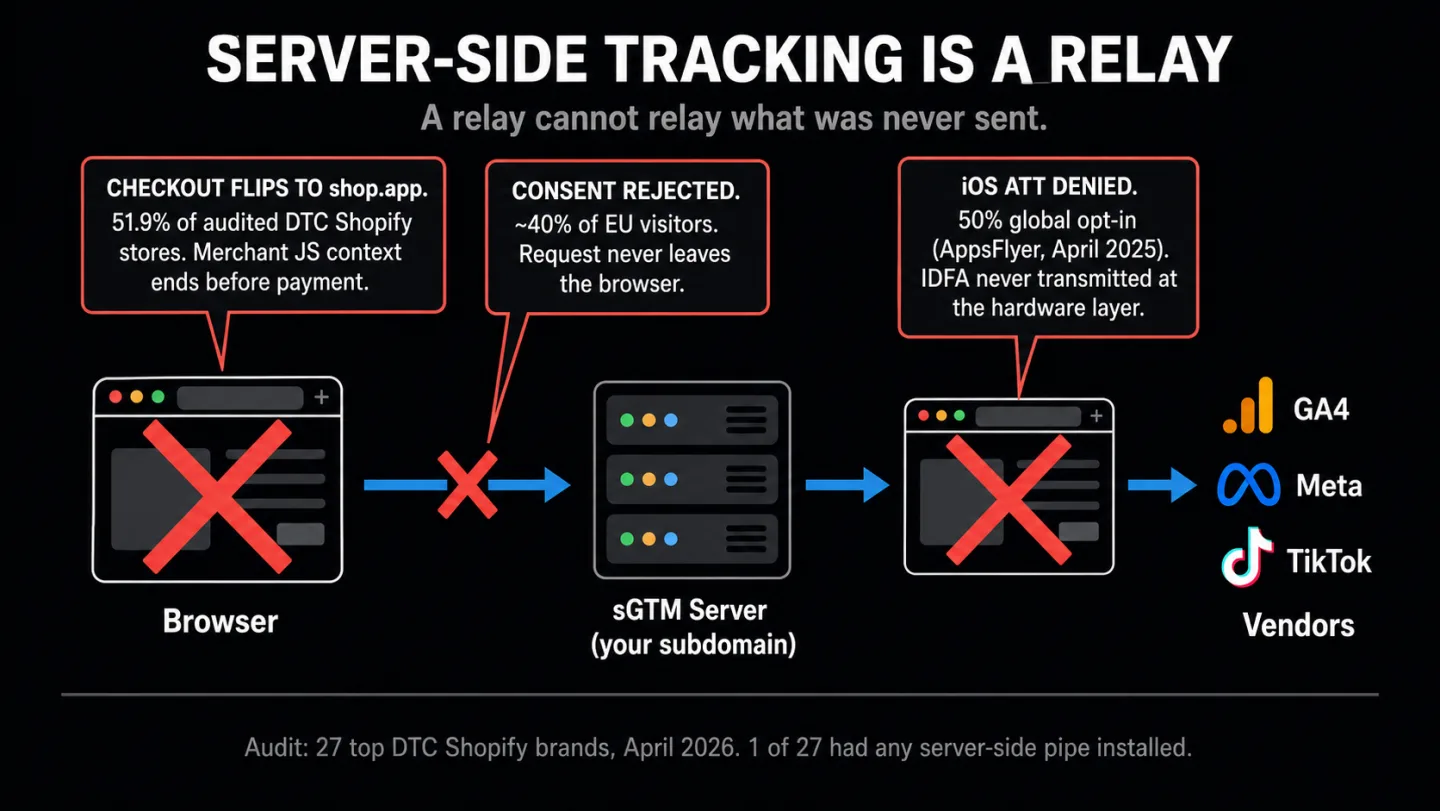
Server-side tracking, also called server-side GTM, sGTM, or server-side tagging, runs the Google Tag Manager container on a server you control instead of inside the visitor's browser. The browser still fires a request. That request lands on your server container. The container then relays the data to Google Analytics, Meta, TikTok, Pinterest, and whatever else is in your stack.
That is the architecture. The architecture is not the confusion. The confusion is what the architecture solves.
Proxy. Not origin. The server-side container is entirely reactive. It waits for incoming HTTP requests from browsers. If the browser never sends a request, because an ad blocker removed the GTM loader, because the user rejected consent and the consent layer suppressed the fire, or because the event happened in a payment sheet the page script cannot see, the server-side container receives nothing at all. There is no magic. A relay cannot relay a message that was never sent.
Google's own documentation in the Measurement Protocol section confirms this framing. The docs explicitly recommend you keep a GA4 tag on your web page to send data to the server container. That is, you still need a browser tag. sGTM changes where data is processed. It does not change how data originates. This is the single most important sentence in this article, and the one every vendor blog glosses over.
googletagmanager.com. Safari's 7-day JavaScript cookie cap truncating your returning-visitor window. Consent Mode v2 cookieless pings not reaching Google.Simo Ahava's 2020 article is still the clearest explanation of the architecture. Julius Fedorovicius at Analytics Mania, the second most-cited independent practitioner on this topic, reinforces the same framing: the browser sends a single request to your server, which then distributes the data to vendors. The word "distributes" is the load-bearing word. Distribution of data presumes data exists to distribute.
The 27-store audit
In April 2026 we crawled the public HTML of 27 top DTC Shopify brands across apparel, beauty, food and beverage, and home goods. Names you would recognize. Every brand in the sample is a recognizable category leader with substantial traffic and an active paid-social presence. We looked for signatures of the four major server-side rescue pipes (Elevar, Stape, Littledata, Analyzify) plus generic custom-subdomain sGTM patterns (tag.*, tags.*, gtm.*, analytics.*, sgtm.*). The full crawl method and the complete list of detection regex is published with the sibling article at /blog/shopify-ga4-revenue-mismatch.
Here is what the re-audit showed when we filtered for server-side adoption specifically.
23 of 27 (85.2%) are fully client-side dependent, with no server-side redundancy of any kind in their publicly visible stack. The average store runs 2.1 distinct client-side tag domains. 14 of 27 (51.9%) have Meta Pixel firing client-side. Two-thirds have PayPal express enabled. 77.8% reference shop.app, pay.shopify.com, or checkout.shopify.com somewhere in their cart or checkout HTML.
This is not a sample of companies that do not know what server-side tracking is. A brand running a seven-figure Meta ad spend has read every Elevar case study. They have had Stape demos. They have seen the 30% data recovery claim. And 26 of them out of 27 have collectively decided the pipe is not worth the money. The rest of this article is why.
What server-side tracking does fix
Before the limitations, give fair credit. Server-side tracking closes a real set of gaps. These are the wins, each traced to a primary source.
/collect shapeSafari's Intelligent Tracking Prevention caps JavaScript-set first-party cookies at 7 days of inactivity. A visitor who returns on day 10 appears as a new visitor. Server-set cookies from a genuine first-party subdomain escape that cap (webkit.org/tracking-prevention). If your checkout assumes durable attribution and your audience skews heavily iOS, this is real recovery.
Ad blockers that target google-analytics.com or connect.facebook.net by domain name miss requests that hit a custom subdomain instead. EasyPrivacy's live filter list confirms rules like ||google-analytics.com^$third-party, which match the hostname, not the path. A request to tag.brand.com does not match any of those rules by default. Stape, Hallam Agency, and several independent practitioners have confirmed this in tests. But it is not permanent. Brave's Shields perform CNAME uncloaking, which follows the DNS chain and blocks the destination anyway. uBlock Origin's filter set includes URL-path patterns like /collect that match the request shape regardless of domain. The sizable share of desktop EU users on simpler domain-matching blockers sees real recovery. The subset running Brave (over 100 million monthly active users as of September 2025, per brave.com/blog/100m-mau) do not.
If your audience skews iOS Safari, if you run paid social at scale, and if your current Pixel and CAPI dedup is clean, server-side tracking will recover attribution that client-side cannot. Stape's own 10-day internal test showed 3.29% of events recovered from ad blockers and 20.71% from Safari ITP mechanisms. Those are real numbers. For a store already capturing 92% of events, adding sGTM recovers a few more percentage points. That is a fair description of the upside.
What server-side tracking cannot touch
Two failure modes the rescue pipes do not advertise because they cannot fix them.
Events that never fire. If a consent management platform suppresses the tag based on the user's rejection, no request leaves the browser. The server-side container has nothing to receive. In Germany and France, roughly 40% of visitors reject cookies when the banner gives them an equally visible choice. The Advance Metrics 2024 study observed 40.6% rejection across 1.2 million interactions on B2B sites spanning Germany, France, Switzerland, and the US. etracker's 2025 benchmark pegs data loss on fully compliant German banners at roughly 60%. Bielova et al. 2024 in USENIX Security ran controlled experiments with 3,947 participants in France and measured 17-47% rejection depending on banner design. None of those rejected sessions are recoverable by sGTM. They originate in a browser state where origin was never permitted.
"Modern privacy regulations are not about technology. They are about consent. If a visitor did not give you consent for tracking, it does not matter how you collect data, client-side, server-side, whatever." (Julius Fedorovicius, Analytics Mania, updated November 2025)
Events that originate on a domain you do not control. Shop Pay, Apple Pay, PayPal express, and iframed 3DS flows complete on shop.app, pay.shopify.com, or the wallet provider's own payment sheet. Your merchant JavaScript stopped executing the moment the buyer tapped the button. sGTM cannot relay what your pages never sent.
This is not a bug. It is how Shopify explicitly designed the Customer Events system. Shopify staff member Alan_G, writing on community.shopify.dev/t/shop-pay-and-web-pixel-events/17696: "it's expected behaviour that the events don't fire in the Shop Pay view." The staff member added that enabling tracking inside the Shop Pay view is "on our radar" for "the medium-term." The thread is from 2024. Nothing has shipped since.
And it is not only Shopify. iOS users who deny App Tracking Transparency never transmit the IDFA to any app at all. Adjust's 2025 benchmark puts industry-wide opt-in at 35%. AppsFlyer's broader post-ATT report (April 2025) shows 50% global opt-in among users who saw the prompt. Either number means a large chunk of iOS users is missing at the device layer, not the network layer. Server-side tracking cannot reconstruct what the hardware never emitted. Nothing can.
The Shopify origination gap
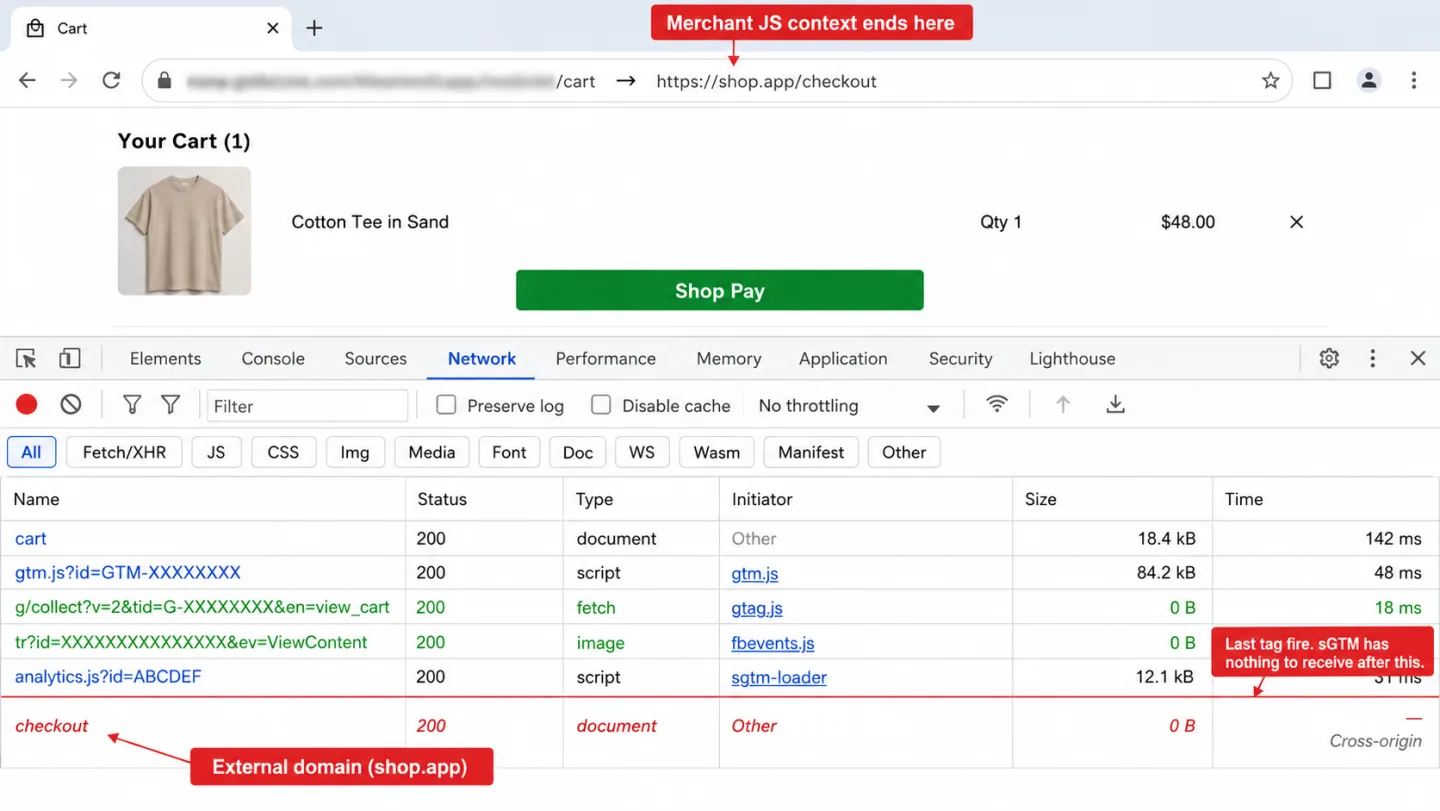
Out of 27 audited stores, 14 (51.9%) run Meta Pixel client-side AND route checkout to an external Shopify domain. In those 14 stores, the Meta Pixel purchase event literally cannot fire in the merchant's JavaScript context. The customer is on shop.app when payment completes. Whatever tag was going to track the purchase was left behind two steps earlier.
shop.app. Your JS context ends here. No more tag fires. The server-side container is still waiting for events.74.1% of audited stores have Shopify's Web Pixel sandbox active. Inside the sandbox, even tags loaded through Shopify's own Customer Events API cannot access the merchant page DOM, cannot directly read localStorage, and cannot reach window.location on the parent frame. Shopify confirms: "App pixels are loaded in a strict sandbox" (shopify.dev/docs/api/web-pixels-api). There is no override. A developer cannot bypass it. This is the supposed "native CAPI alternative" that rescue-pipe vendors pitch as the answer, and even it does not have the access people think it does.
The one event that fires reliably regardless of checkout path is orders/paid, a server-to-server webhook Shopify sends from their backend the moment payment is confirmed. No browser. No JavaScript. No consent context. No sandbox. That webhook is what origin-first analytics listens to instead of waiting for a relay. More on that in section nine.
What the rescue-pipe ecosystem actually costs in 2026
We pulled every pricing page live on April 15, 2026. Here is the real number.
| Vendor | Entry | Mid-tier | Top tier | Setup fee |
|---|---|---|---|---|
| Elevar | $0 (100 orders) | $200-$450 | $950 | $1,000+ |
| Stape | $0 (10K req) | $17-$83 | $167 | None |
| Littledata | $0.35/order | $199-$449 | $990 | None |
| Analyzify | $109 | $206 | Contact | $295 + $1,490-$2,790 sGTM add-on |
| Addingwell (EUR) | €0 (100K req) | €90-€210 | €1,190 | None |
Honest math for a mid-traffic Shopify store at roughly 500,000 monthly site requests and 5,000 monthly orders, wanting Meta CAPI plus durable GA4 attribution:
- Elevar Growth tier: $450/mo
- Stape Pro tier for sGTM hosting (500K requests): $17/mo
- Stape Meta CAPI Gateway pay-as-you-go: $8/mo per pixel
- Elevar Expert Installation: $1,000 one-time
Ongoing: $475/mo. Setup: $1,000. If you swap Elevar for Analyzify, the setup cost rises to $295 plus the $1,490 to $2,790 sGTM add-on. If you swap for Littledata Pro, the ongoing rises to $449/mo. If you go DIY on Google Cloud Run, Google's own infrastructure planning doc cites approximately $50 per instance per month with a three-instance minimum for production redundancy, so $150/mo before logging and before the analytics engineer who owns the pipeline. seresa.io's analysis, "The True Cost of GTM Server-Side Is Not Just $90 Per Month," adds another $100 to $500/mo for ongoing logs and maintenance.
Call the realistic total $500 to $600 ongoing plus $1,000 to $2,000 setup for a managed deployment. Now ask what that recovers. Stape's own internal 10-day test reported 3.29% of events recovered from ad blockers and 20.71% from Safari ITP. Real numbers. For a store capturing 92% of events client-side, adding server-side recovers another 4-6%. For a store at 70% (heavy EU consent rejection plus ad blockers), server-side recovers maybe 10% more, leaving the 20% consent gap untouched. The honest ROI question is whether that recovery pays for the pipe. For some stores it does. For 26 of 27 audited here, the math evidently does not.
The EMQ ceiling
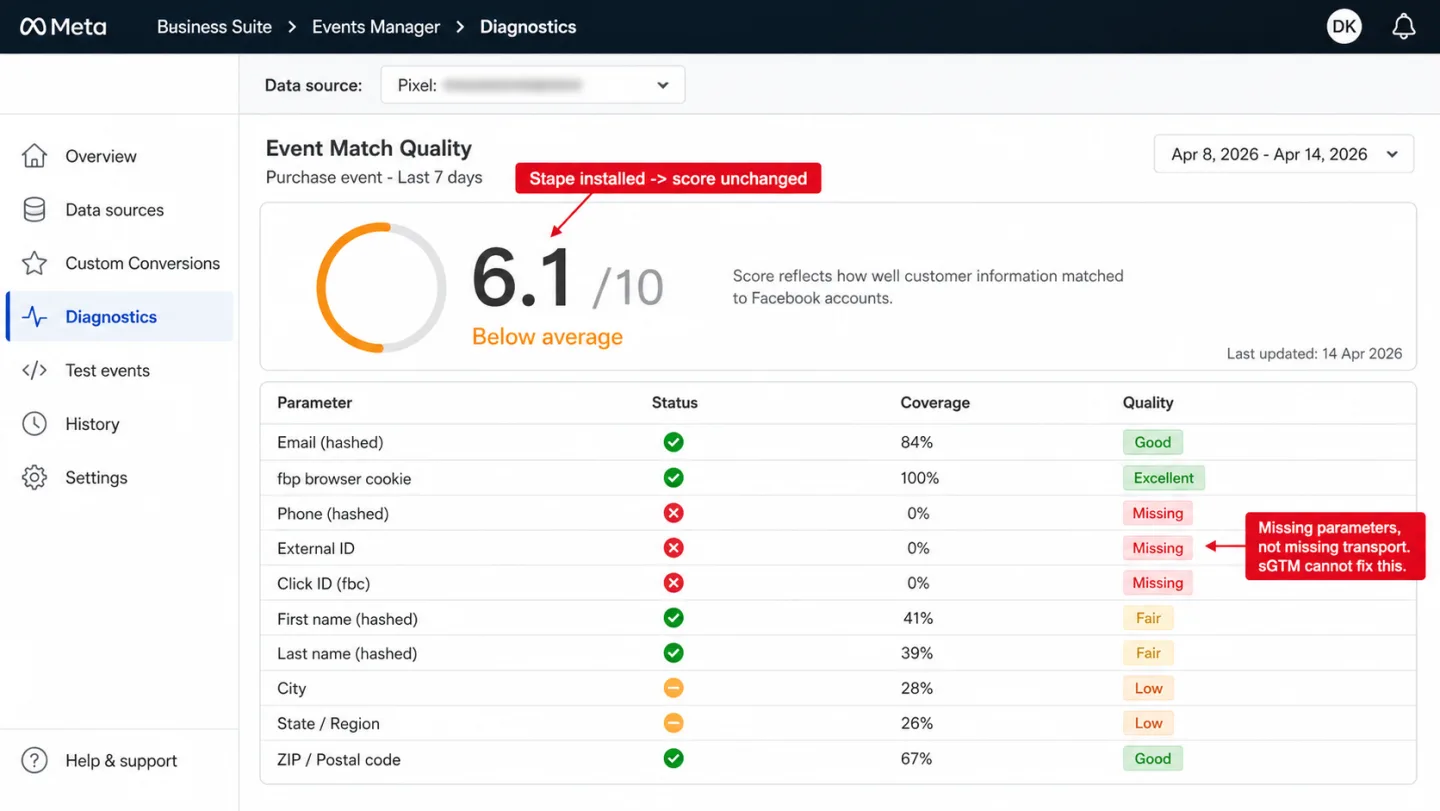
Meta's own best-practices documentation is explicit: "Event Match Quality is available for web events" and reflects how effectively customer information can be matched to a Facebook account. The parameters that move the needle, in descending priority per CustomerLabs benchmarking, are hashed email, hashed phone, a full name-address-city-state-zip block, external ID, click ID, and the fbp browser cookie. Transport mechanism is not on that list.
A recurring frustration pattern from r/FacebookAds and the Stape community forum: an operator installs GTM plus Stape over three days expecting a 10/10 EMQ and ends up stuck at 6.1. One Reddit commenter in that thread summarized the cause directly: EMQ depends on how many parameters you send to Meta, not on whether transport runs server-side. GTM plus Stape by themselves do not increase EMQ. Another operator in a separate thread on CAPI migration (thread 1ske0xw) saw event coverage drop to 0% and CPA double after switching providers, with the new provider insisting the dedup failure was "completely normal."
Dedup between the pixel and CAPI is the other hidden failure mode. Meta deduplicates by matching event_id and event_name within a 48-hour window. If either side is missing the event_id, or if the IDs are generated differently client-side vs server-side, the same conversion counts twice. A Shopify Community thread from March 2025 (t/purchase-event-from-the-server-are-not-deduplicated/401366) documents systemic dedup failures across AddToCart, InitiateCheckout, ViewContent, and Purchase simultaneously because no event_id parameter was being sent. Those stores over-reported conversions for weeks and their Meta auto-bidding optimized to the inflated number. The damage was real.
The decision framework
Rather than generalizing, here is a short scorecard. Six questions, personalized verdict.
Origin-first: what the architecture looks like when events come from the server by design
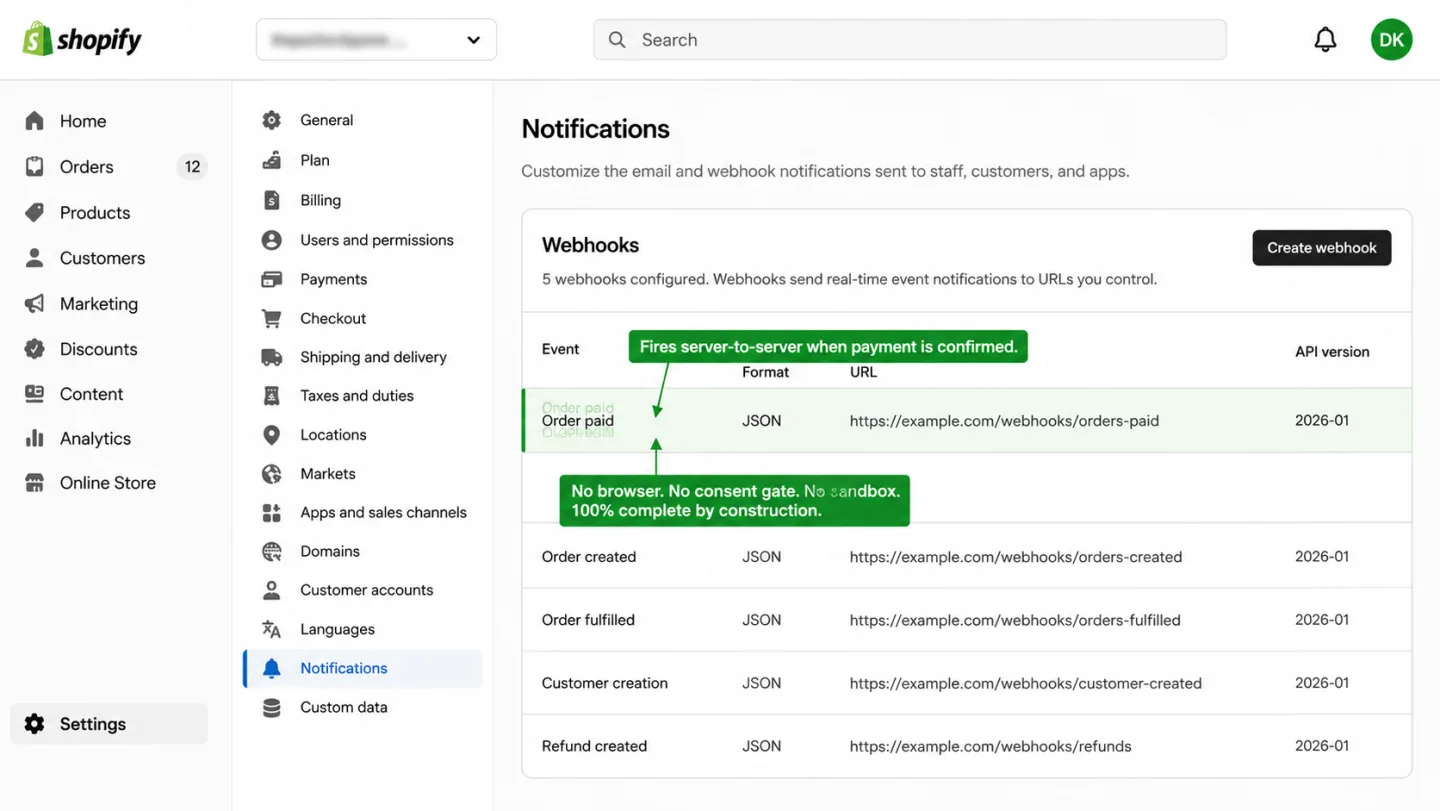
There is a different architecture. Not a transport relay. An origin-first architecture where the events that matter originate on the server, full stop, and the browser is an optional signal rather than the load-bearing one.
Shopify publishes an orders/paid webhook that fires when payment is confirmed. No browser involvement. Every order fires it: Shop Pay, Apple Pay, PayPal, standard card, B2B invoice, subscription renewal. A webhook-driven purchase signal is 100% complete by construction. The customer could close their tab mid-checkout and the signal still fires. Ad blockers have nothing to block. Consent banners have nothing to gate. There is no client-side script to relay.
The same pattern exists beyond Shopify. WooCommerce has a woocommerce_payment_complete action hook that fires server-side on completion (we audited 75 WooCommerce stores and not one of the tracked ones had a server-side net in place). Stripe has a payment_intent.succeeded webhook. PayPal, Square, Adyen, and every modern processor emit equivalent server-side events. A headless storefront with a custom checkout backend can emit its own completion webhook. What these have in common is that the purchase signal originates where the data actually lives, on a server, not where a tag happened to fire, in a tab that might not even be open anymore.
That is what Clickport is built around. The tracker is first-party and cookieless, so ITP and ad blockers have no meaningful impact on what it captures for sessions, sources, and channels. (For why the privacy-friendly client-side category dodges most of the failures discussed above, see our privacy-friendly analytics guide.) And because Clickport exposes a Custom Events API, your server-side order handler can fire the purchase event directly, one line of code, no CNAME, no Cloud Run container, no $1,000 expert installation, no EMQ to monitor, no dedup window to configure:
clickport.track('Purchase', { order_id: '12345' }, { revenue: 89.00 })
Call it from your Shopify webhook handler, your WooCommerce action, your Stripe webhook receiver, or your own backend. The purchase attaches to the landing session source Clickport already captured for that visitor, with no Meta Pixel setup, no CAPI bill, no sandboxed web-pixel adapter. If you are reading this because your GA4 and Shopify admin do not match and you are staring down a $600 per month Elevar quote, the architectural question is worth asking before you sign the contract.
The honest verdict
Server-side tracking is not a scam. For the specific subset of stores where client-side tags fire cleanly, where Safari ITP is breaking attribution on a high-iOS audience, where the ad spend is large enough that 3-5% recovery pays for the pipe several times over, and where the checkout is fully on your own domain, sGTM earns its keep. There is a real addressable gap, and the pipe closes a meaningful slice of it.
For the 26 of 27 top DTC Shopify brands we audited in April 2026, the math did not work. Not because they do not know what server-side tracking is. Because they do.
The question is not "how do I move my tag to a server." The question is "where do my purchase events originate." If they originate in shop.app, no pipe closes the gap. If they originate in a consent-rejected session, no pipe closes the gap. If they originate in an iOS app where the user declined ATT, no pipe closes the gap. If they originate on a server you control, you do not need the pipe in the first place.
Pick the architecture that matches where the data actually lives.
Frequently asked questions
Is server-side tracking legal?
Yes, the architecture itself is legal. The legal question is whether your specific implementation respects the same GDPR, ePrivacy, CCPA, and consent obligations that apply to any tracking. Moving processing from the browser to your server does not remove your data-controller responsibilities. If a visitor in the EU has rejected non-essential cookies, your server-side container should not process their data, regardless of how that data arrived. The Norwegian Datatilsynet, France's CNIL, and Germany's BfDI have all stated that server-side tracking inherits the legal status of the data being relayed. If the underlying data is personal and there is no lawful basis, server-side does not fix it. If the underlying data is genuinely anonymous and aggregate, server-side is fine. The architecture is neutral; the implementation is what regulators look at.
What is the difference between server-side tracking and server-side tagging?
In practice the terms are used interchangeably, though strictly speaking server-side tagging is the narrower term. Server-side tagging refers specifically to managing tag containers (most commonly Google Tag Manager Server-Side, sGTM) on a server you control. Server-side tracking is the broader category and includes server-side tagging, direct server-to-API integrations (Meta CAPI, Google Enhanced Conversions), webhook-driven event capture (Shopify orders/paid, Stripe payment_intent.succeeded), and analytics tools that ingest events from any backend source. Most vendor blogs use "tracking" and "tagging" loosely. When someone says "we set up server-side tracking", they usually mean sGTM specifically. Synonyms you will encounter in the wild: SST (server-side tracking), backend tracking, tagless tracking, server-side analytics.
Does server-side tracking bypass ad blockers?
Partially. Blockers that match known vendor domain names like connect.facebook.net or google-analytics.com miss requests that hit a custom subdomain instead. Blockers that match URL path shapes like /collect still catch sGTM requests. Brave's Shields perform CNAME uncloaking to defeat the subdomain trick. uBlock Origin targets request shape, not just hostname. The baseline ad-blocker recovery from sGTM on a well-configured custom domain is around 3-7% of blocked events per Stape's own internal test, not the 30% figure rescue-pipe vendors commonly advertise.
Is server-side tracking GDPR compliant by default?
No. Julius Fedorovicius at Analytics Mania states it plainly: "Server-side does NOT make you automatically GDPR/CCPA/etc. compliant." If the user rejected consent, your server-side container should not be processing their data regardless of how the data was collected. Moving data flows to the server layer actually increases your data-controller responsibility, not decreases it. Simo Ahava's 2022 piece makes the same argument from the transparency side: "Moving data flows server-side makes it more difficult to validate if the data is collected and processed legally and according to the user's wishes and choices."
How much does server-side tracking really cost in 2026?
Honest managed deployment for a mid-traffic Shopify store: roughly $541-$970 per month ongoing plus $1,000-$2,790 in initial setup. That covers Elevar or Littledata for the Shopify data layer, Stape for sGTM hosting, and the Meta CAPI Gateway. DIY Google Cloud Run is cheaper on infra ($150/month for a 3-instance production setup) but requires a dedicated analytics engineer to build and maintain, so total cost of ownership typically rises once engineering time is priced in.
What is the difference between sGTM and Meta CAPI?
sGTM is the transport layer. Meta CAPI is one of the destinations it sends to. You can send Meta CAPI events without running sGTM (direct server-to-API integration). You can run sGTM without sending to Meta. Many stores run both together: sGTM as the container, CAPI as one vendor client inside it. The dedup mechanism (matching event_id plus event_name within 48 hours) is a Meta-side construct that applies whether the server call comes from sGTM, from a direct integration, or from Stape's standalone CAPI Gateway product.
Will server-side tracking fix my Shopify and GA4 revenue mismatch?
Depends on the root cause of the mismatch. If the gap is Safari ITP and ad blockers, sGTM helps. If the gap is Shop Pay, Apple Pay, and PayPal express checkouts completing on external domains, sGTM does not help. Our 27-store audit found the express-checkout gap affects 77.8% of sample brands. The transport fix addresses a smaller slice of the gap than most vendor pages imply. The mismatch article has the full breakdown.
Can I use server-side tracking without Google Tag Manager?
Yes. Server-side GTM is one implementation. Other options: direct server-to-API integrations with Meta CAPI, Google Enhanced Conversions, and similar endpoints. Cookieless first-party analytics tools like Clickport receive events from webhooks, which is origin-first rather than server-side-relay. The "server-side" category is broader than sGTM specifically.
What's the difference between server-side tracking and cookieless analytics?
Server-side tracking refers to where the tag runs (on your server vs. in the browser). Cookieless analytics refers to whether persistent identifiers are used at all. They are orthogonal. An sGTM setup typically still uses first-party cookies (that's part of its value proposition: longer-lived cookies). A cookieless analytics tool does not set persistent identifiers anywhere, client or server. Vendor blogs sometimes conflate the two. They are different architectural choices with different privacy implications.
Stop paying for the relay
The pipe only helps if the problem is transport. For most DTC Shopify stores in 2026, the larger problem is origination: events that never fire because the user rejected consent, events that fire in shop.app where your merchant JavaScript cannot run, events that never leave an iOS device because the user declined ATT.

Comments
Loading comments...
Leave a comment